
Two-factor authentication (2FA) has become standard practice for increasing security for access to high-risk or high-value areas. There is almost always a built-in delay caused by requiring two factors of authentication to enter a space. It takes time to swipe your badge, enter a PIN code or scan a fingerprint. Although these delays may seem small, they can add up significantly over time and across a large group of people. There is also the inconvenience when one is trying to carry items such as one's computer, boxes, or other materials.
In this post, we’ll examine pitfalls common to most two-factor solutions. We’ll also show that by applying facial authentication as the second factor, the experiences for the user can become frictionless.
Legacy technology
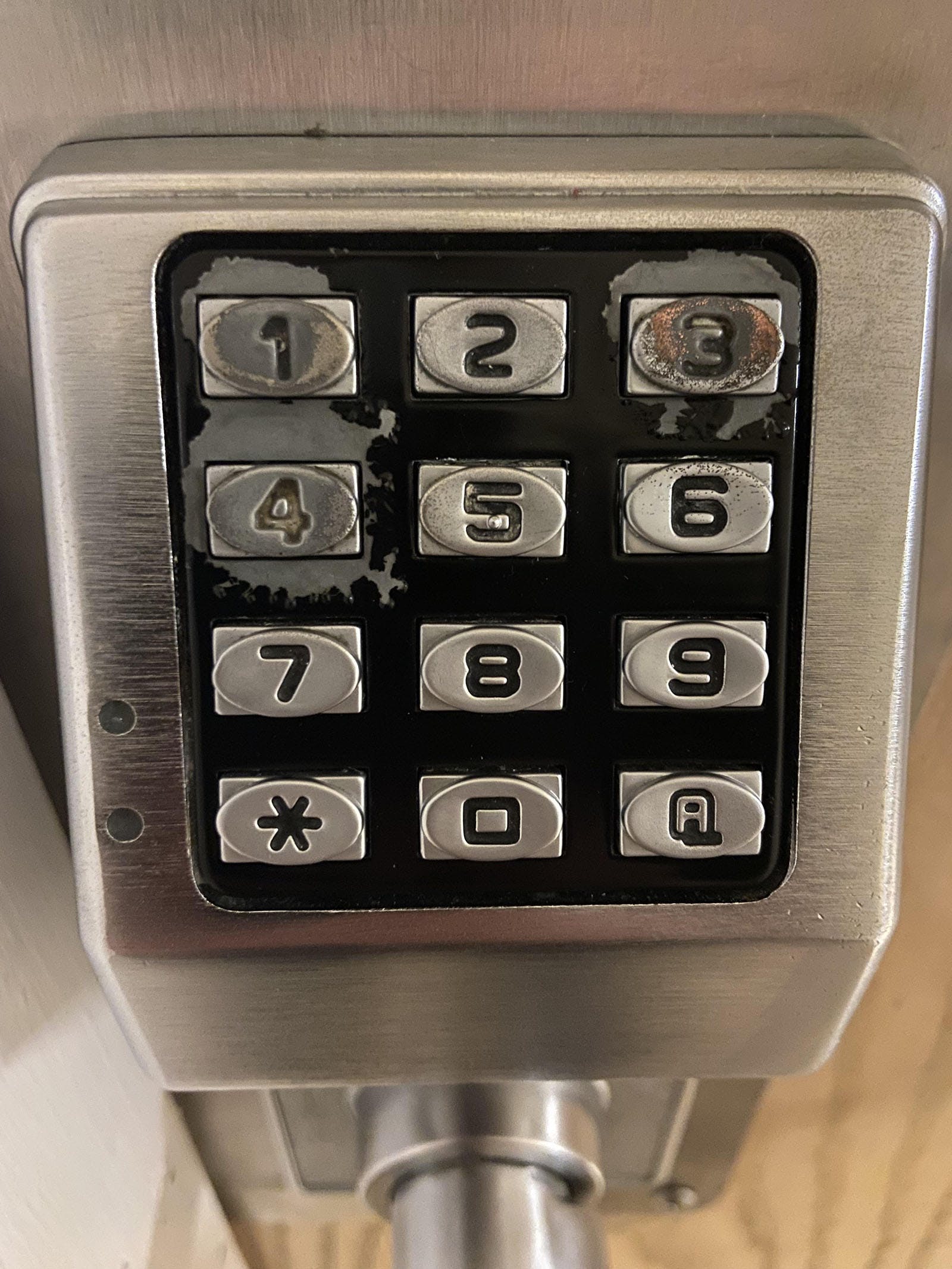
Traditional access cards are prone to be lost, stolen, copied, or shared. It is estimated that the average enterprise company replaces 10-15 percent of their employees' badges each year. PIN codes are also vulnerable to being shared or “learned” by bad actors who watch at a distance and can see the digits of a code being entered or figure out the “wear and tear” on the keypad. Card readers that include a keypad are better than simple standalone readers, but most security experts would agree they are not as highly secure as desired.
Early biometrics
Early fingerprint and palm biometrics are a viable second-factor technology for two-factor authentication. While these readers can be more difficult to spoof, they have been fooled.
Fingerprint biometrics can be fooled in a number of ways, including the use of fake fingerprints made from materials such as silicone or playdough, or by using a high-resolution image of a fingerprint to create a replica. Another method is called "spoofing" where an attacker uses a mold or a lifted fingerprint to create a replica.
Iris readers are another biometric option as a second factor for authentication. In the right conditions, these readers are highly accurate. The downside is that they require assisted enrollment and don’t work for everyone. For example, some individuals may have had eye surgery or injury that has altered their iris patterns. Users may also become frustrated as they need to move their heads in and out to get a valid read.
These technologies also do not work well for all people. Plus, in the post-pandemic world, all of these platforms require you to touch the surface of a reader, which increases the spread of germs.
Modern facial biometrics can reduce friction
There is modern solution. Facial authentication allows you to significantly reduce – if not eliminate friction while providing a more secure method of authentication than all methods discussed above. With facial authentication, you don't need to slow down to access an area. Facial authentication instantly authenticates the user using the power of artificial intelligence and edge-based computing. All-in-all, this leads to reduced friction, faster throughput, improved efficiency, and an improved user experience.

The Alcatraz AI Rock compares the face of the person in front of the reader against a database of 25,000 user templates to find the match in less than one second. It begins to read the face as you approach the door, so often your face is authenticated as you reach your badge out toward the card reader.
The algorithm employed by Alcatraz AI can be effectively used by everyone, unlike iris, fingerprint, or palm technologies. There are no delays caused by time spent aligning your eyes or hands to the detection areas of the reader. This extra time, which can cause significant delays for iris, fingerprint, or palm readers, is saved by using facial authentication.
Finally, with the Rock, your access control becomes touchless. PIN pads, fingerprint, or palm scanner surfaces can be home to bacteria and germs or spread infectious diseases, like colds, flus, or COVID-19.
The Alcatraz AI Rock allows users to get all of the security benefits of two-factor authentication at the speed of single-factor.
Contact Alcatraz AI to learn more about how your company can reduce friction in 2FA environments.
← Previous -- Next →
Tag(s):
Blog
Other posts you might be interested in
View All Posts
Blog
3 min read
| July 31, 2025
Executive Protection Isn’t Just for High-Risk Industries Anymore
Read More
Blog
16 min read
| June 11, 2025
Data Center Security: Why Facial Authentication is the Ultimate Second Factor in a Zero Trust World
Read More
Blog
3 min read
| June 20, 2023
Exploring Privacy and Security with Facial Biometrics
Read MoreSubscribe to email updates
Additional content around the benefits of subscribing to this blog feed.


